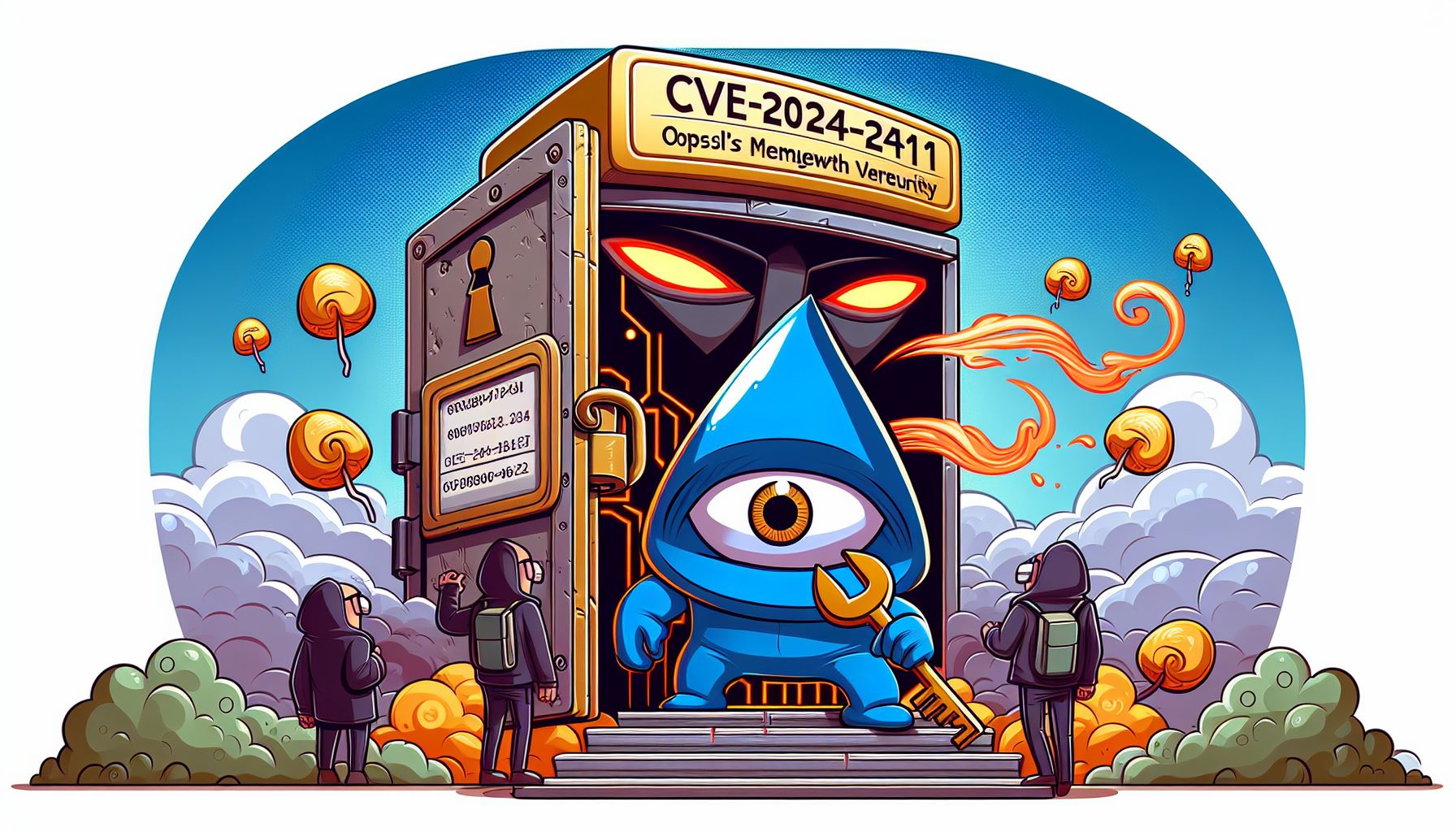
Unveiling the Intricacies of CVE-2024-2511: A Deep Dive into OpenSSL's Memory Growth Vulnerability
Unveiling the Intricacies of CVE-2024-2511
🔐 Unlocking the Secrets of Crypto Math: Your Guide to Secure Digital Adventures 🔢🚀
Welcome to our captivating journey into the world of cryptography, where math meets mystery and security. In our “Crypto Math Series,...
Read MoreAll Stories
Unveiling the Intricacies of CVE-2024-2511: A Deep Dive into OpenSSL's Memory Growth Vulnerability
Unveiling the Intricacies of CVE-2024-2511
In security, Network Security, Apr 12, 2024Unveiling the SSH Terrapin Attack: A New Threat to Network Security
The Secure Shell (SSH) protocol, a cornerstone of secure network administration, faces a new cryptographic challenge known as the Terrapin Attack. This sophisticated threat manipulate...
In Cybersecurity, SSH, Network Security, Jan 01, 2024Securing the Future: X25519 and Kyber768's Role in Thwarting Quantum Threats 🛡️🚀
As the quantum computing era looms, the cryptography world is pivoting towards algorithms that can withstand the unprecedented computational power of quantum computers. This is the do...
In Post-Quantum, X25519, Kyber768, Dec 10, 2023Decoding Signature Algorithms: RSA vs. ECDSA, A Technical Deep Dive 🕵️♂️🔍
Digital signatures are crucial for ensuring the integrity and authenticity of data in our increasingly digital world. In this post, we’ll conduct a technical comparative analysis of m...
In cryptography, digital signatures, Dec 09, 2023🗝️🔐💻 Unraveling the Mysteries of Key Exchange Protocols: A Comprehensive Guide
Secure communication in the digital world hinges on the robustness of key exchange protocols. These protocols are the backbone of private communication, enabling the secure exchange o...
In cryptography, key exchange, Dec 09, 2023Integrating OpenSSL with OQS Providers for Enhanced Quantum-Safe Security
In the rapidly evolving landscape of quantum computing, ensuring quantum-safe security protocols is more critical than ever. OpenSSL, a widely used toolkit for SSL and TLS protocols, ...
In security, OpenSSL, OQS, Quantum-Safe, Dec 06, 2023Unlocking the Power of ICAP Protocol: A Comprehensive Guide 🌐💡
Introduction
In ICAP, Proxy, Nov 05, 2023🚀 Unlocking the World of Secure Communication with DH Groups and Certificates 💻🔒
🚀 Unlocking the World of Secure Communication with DH Groups and Certificates 💻🔒
In Cryptography, Security, Oct 30, 2023Demystifying the IoT Ecosystem: Roles, Vendors, Challenges, and Solutions
🌐 In an increasingly data-driven world, the Internet of Things (IoT) stands as a transformative force. IoT empowers us to connect and harness data from an array of sensors and devices...
In IoT, Technology, Oct 07, 2023🔐 Decoding the Magic: Unveiling the Difference Between Lightweight and Heavyweight Ciphers 🚀 - A Journey Into Cryptographic Worlds 🌐
Unlock the secrets behind lightweight and heavyweight ciphers in this captivating exploration! 🧐 Discover why these cryptographic powerhouses exist, their impact on security, and how ...
In Cryptography, Security, Sep 30, 2023Featured
-
Securing the Future: X25519 and Kyber768's Role in Thwarting Quantum Threats 🛡️🚀
In Post-Quantum, X25519, Kyber768, -
Decoding Signature Algorithms: RSA vs. ECDSA, A Technical Deep Dive 🕵️♂️🔍
In cryptography, digital signatures, -
🗝️🔐💻 Unraveling the Mysteries of Key Exchange Protocols: A Comprehensive Guide
In cryptography, key exchange, -
Integrating OpenSSL with OQS Providers for Enhanced Quantum-Safe Security
In security, OpenSSL, OQS, Quantum-Safe, -
🔐 Decoding the Magic: Unveiling the Difference Between Lightweight and Heavyweight Ciphers 🚀 - A Journey Into Cryptographic Worlds 🌐
In Cryptography, Security, -
Demystifying Lightweight Cryptography: A Necessity for a Connected Future
In Cryptography, Security, -
🔐 Unlocking the Secrets of Crypto Math: Your Guide to Secure Digital Adventures 🔢🚀
In Crypto-Math-Series, -
Exploring the Landscape of Popular Phishing Frameworks
In security,